Recent Posts
Why Private Domain Data Is the Real Key to AI That Actually Works
Every enterprise racing to deploy AI hits the same wall eventually: the outputs are technically impressive but commercially useless. The model knows everything about everything and nothing about your business. That gap — between general capability and contextual intelligence — is a data problem, and it’s the problem KeyAPI.ai is built to solve.
The Generic AI Problem Is a Data Problem
General large language models are trained on public datasets. That makes them broadly knowledgeable and entirely generic. Ask one to help with e-commerce user preference analysis, social media content strategy, or brand marketing targeting, and it will produce polished, plausible, competely undifferentiated output. It has no idea what your customers actually buy, what your community actually says, or what your competitors are actually doing.
Orkes Raises $60M to Bring Production-Grade AI Orchestration to Enterprise Developers
Orkes, the workflow and agent orchestration platform founded by the original engineers behind Netflix’s microservices infrastructure, has closed a $60 million Series B round led by AVP, with participation from Prosperity7 Ventures, Nexus Venture Partners, Battery Ventures, and Vertex Ventures US. The raise signals growing enterprise demand for orchestration infrastructure that can take AI workloads from prototype to production without falling apart.
The company’s foundation is Conductor, an open-source orchestration engine originated at Netflix in 2016 and still actively maintained by Orkes. Netflix’s own internal usage of Conductor has grown fivefold in recent months, and the project counts developers at JP Morgan Chase, Tesla, Atlassian, Oracle, American Express, and GE Healthcare among its users. Since its $20 million Series A in 2024, Orkes has tripled its paying customer base and built a developer community in the hundreds of thousands.
Form.io Launches MCP Server and Agentic Coding Toolset for Governed Enterprise AI Development
Form.io has released an MCP Server, Skills library, and Agentic Coding Plugin designed to bring schema-governed infrastructure to AI coding environments — extending its existing Universal Agent Gateway into the build-time layer. The toolset targets enterprise development teams using agentic coding tools such as Claude Code, Cursor, and Windsurf, where the default outcome is speed without standardization.
The problem Form.io is addressing is real and increasingly visible. As agentic coding accelerates across large organizations, applications generated by independent teams diverge in architecture, data handling, and compliance posture. Each agent makes its own decisions; five teams produce five incompatible implementations of the same solution. The efficiency gains nominally promised by agentic coding are offset by the governance overhead required to manage the fragmentation afterward.
Appdome Upgrades MobileBOT Defense With Identity-First Mobile API Protection
Appdome has released six major upgrades to its MobileBOT Defense product, repositioning it as what the company calls the industry’s first full-suite Identity-First Mobile API Protection solution. The update moves the product’s security model away from probabilistic behavioral inference and toward deterministic cryptographic proof — a distinction that has become commercially significant as AI-generated attack tooling has made legacy bot detection increasingly easy to defeat.
The core architectural shift is the introduction of a multi-tiered identity model that governs every API session before access is granted. Prior generations of mobile bot defense relied on web application firewall heuristics and session cookies to infer whether an incoming request was legitimate. That model has a structural weakness: session cookies can be captured and replayed, and applications instrumented with WAF anti-bot SDKs can be repackaged and run inside automated environments. Appdome’s new approach requires that the identity of the application, the device, and the session be cryptographically verified before any API response is issued.
Five SDK Generators Compared: Speakeasy, Stainless, Fern, APIMatic, and OpenAPI Generator
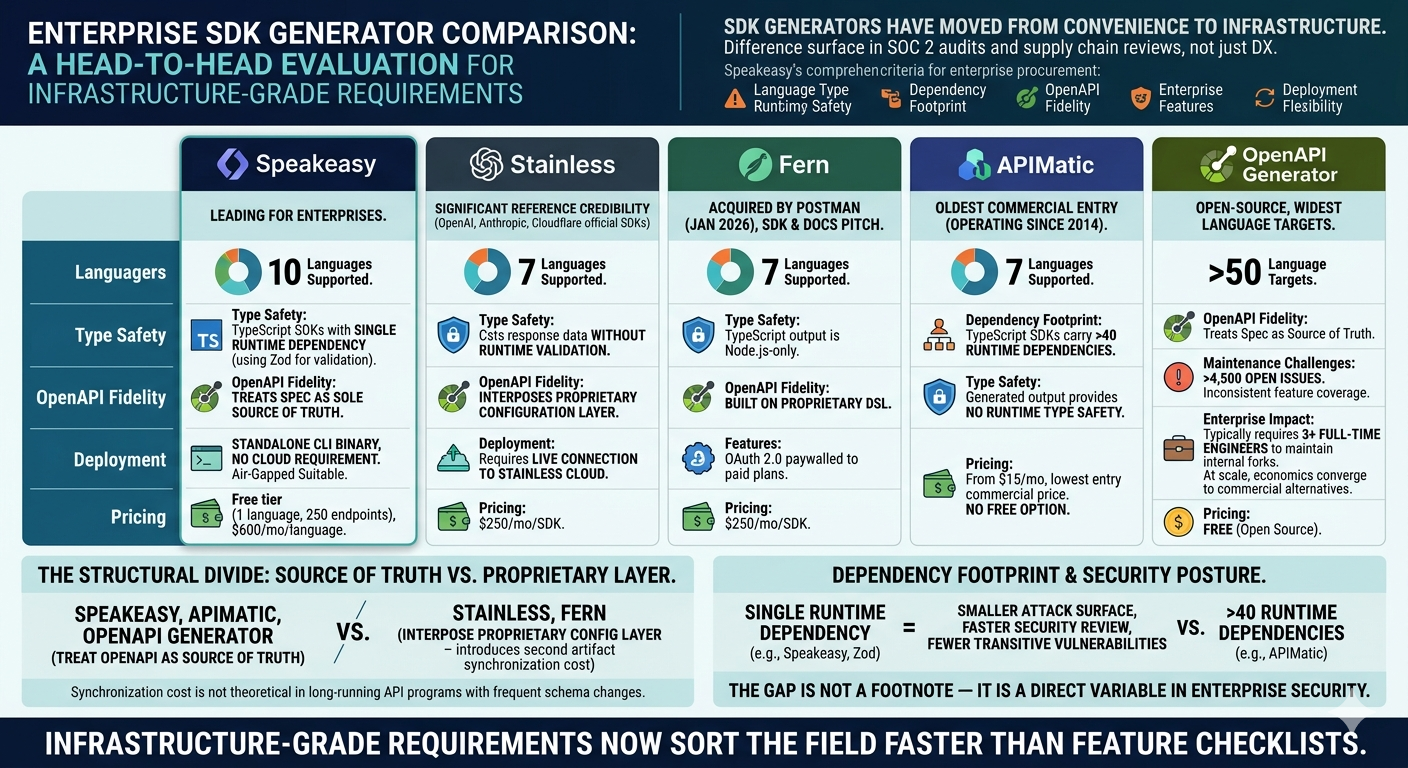
Speakeasy has published a head-to-head comparison of the five most widely deployed SDK generators for OpenAPI specifications, covering Speakeasy itself alongside Stainless, Fern, APIMatic, and the open-source OpenAPI Generator. The evaluation spans language coverage, runtime type safety, dependency footprint, OpenAPI fidelity, enterprise feature sets, and deployment flexibility — the criteria that now determine whether an SDK generator clears enterprise procurement rather than just developer preference.
SDK generators have moved from convenience tooling to infrastructure. API-first companies, including those building for AI agent integrations, now treat generated client libraries as a production artifact, and the differences between generators surface in SOC 2 audits and supply chain reviews rather than only in developer experience surveys.
API Monetization Models That Work and the Ones That Drive Developers Away
API monetization is the discipline that sits at the intersection of product design, pricing strategy, and developer experience. Getting it wrong does not just reduce revenue — it drives away the developers whose integrations would have generated long-term value, in favor of short-term extraction that destroys the developer relationship before it matures.
The history of API monetization is populated with cautionary examples: pricing changes that broke the economics of applications built on the API, free tier eliminations that forced migrations at scale, metered pricing structures that made costs unpredictable enough that developers chose self-hosting over consumption. Each of these is a failure of the same kind — pricing that prioritized the API provider’s short-term revenue over the long-term value of developer trust.
gRPC in Production: What the Documentation Doesn't Tell You
gRPC documentation is thorough on the protocol’s features and sparse on the operational realities of running it at production scale. The gap between the getting-started experience and the production experience is wide enough to have surprised most of the teams that have made the journey. The surprises are not fatal. They are the kind that would have been useful to know before the architecture decision was made.
The gRPC pitch is compelling: Protocol Buffers serialization that is faster and smaller than JSON, HTTP/2 multiplexing that reduces connection overhead, generated client and server stubs that eliminate serialization bugs, strong typing that catches integration errors at compile time rather than runtime. All of these benefits are real. All of them come with operational requirements that the pitch does not emphasize.
Event-Driven Architecture vs Request-Response: Choosing the Right Communication Pattern
The choice between request-response and event-driven communication patterns is one of the most consequential architectural decisions in distributed system design. It determines how services couple to each other, how failures propagate, how the system scales under load, and how difficult it is to trace the flow of data through the system when things go wrong. Most teams treat it as a technology choice — Kafka versus REST — when it is primarily a design choice about how services should relate to each other.
The Business Case for Internal APIs That Most Engineering Leaders Ignore
Internal APIs — interfaces between services within an organization’s own systems — receive less design attention than public APIs because they lack the external consumer accountability that forces quality. The teams that consume internal APIs are colleagues, not customers. Breaking changes can be coordinated by Slack message rather than deprecation notice. Documentation is optional when the API author sits nearby.
The organizations that operate this way accumulate a specific kind of technical debt: internal integrations that are brittle, undocumented, and implicitly coupled to implementation details that were never meant to be part of the interface. The cost of this debt is the engineering time spent maintaining integrations that should be stable, debugging failures caused by undocumented behavior changes, and slowing down service evolution because teams are afraid to change APIs that other teams depend on in ways nobody has mapped.
Breaking Changes: How to Avoid Shipping Them and What to Do When You Must
A breaking change is any modification to an API that requires consumers to update their integration to continue functioning. The definition is straightforward. The practice of avoiding breaking changes while evolving an API requires engineering discipline that most teams underestimate until they have shipped a breaking change to a production API and experienced the resulting incident response.
The instinct to avoid defining something as a breaking change is strong. Removing a field that is not documented is tempting to classify as cleanup rather than a breaking change. Changing an error code from 400 to 422 for a validation failure seems like a trivial semantic correction. Adding a required field to a request body seems like a new feature rather than a breaking change. Each of these reclassifications is wrong, and each produces consumers whose integrations fail after the change.